For years, Skype was widely considered one of the most secure communication platforms in the world.
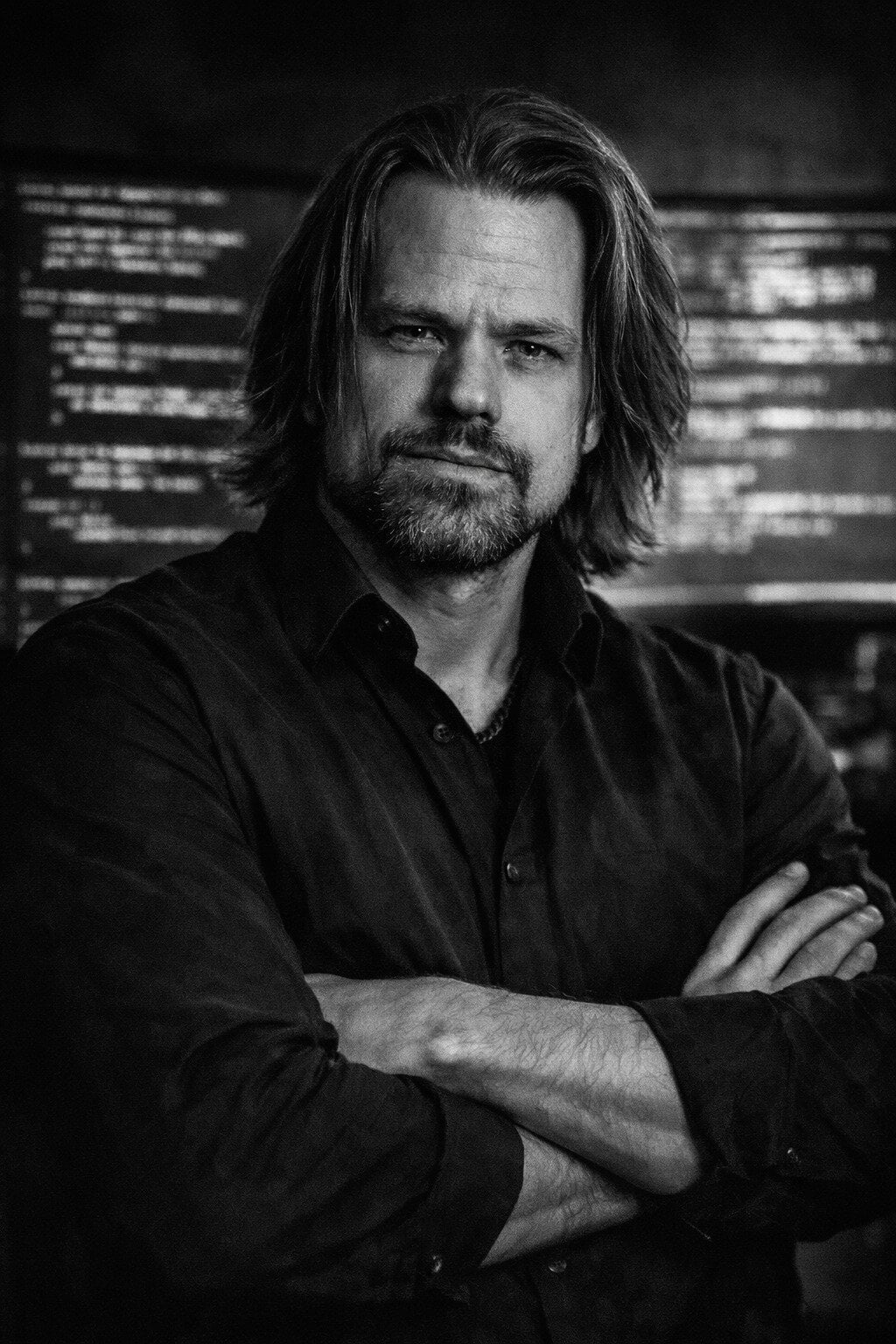
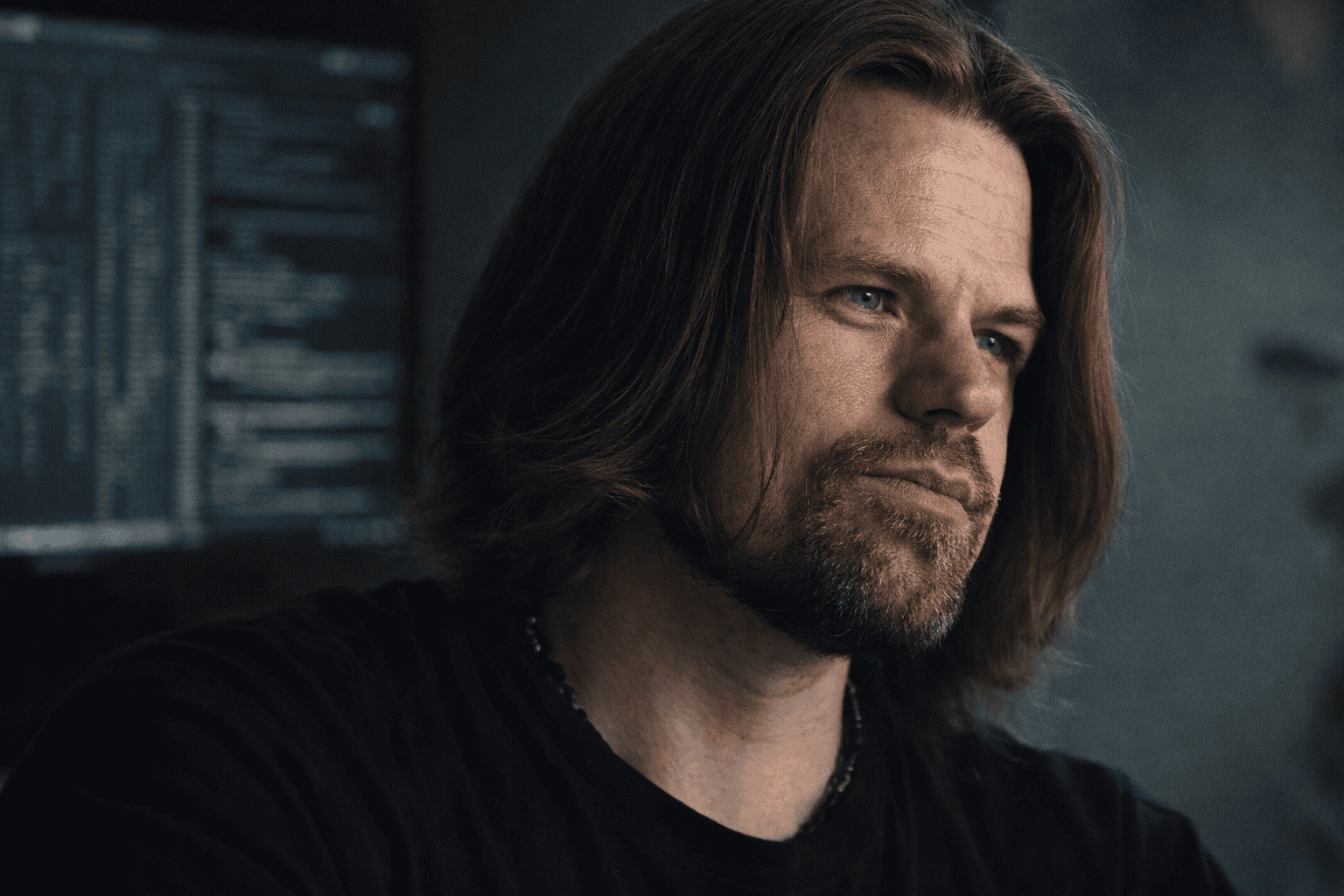
Our CTO, Joel Eriksson, decided to find out if that was actually true.
Beginning in 2004, he reverse-engineered Skype’s architecture — unpacking obfuscated binaries, bypassing anti-debugging protections, extracting cryptographic material, and building tools to inspect encrypted traffic.
What started as curiosity turned into years of deep protocol-level insight into how Skype’s peer-to-peer system actually worked.
In a new article, Joel shares that story — and what it taught him about how secure communication systems should really be built.
Read the full story here:
https://armainstruments.com/the-mystery-of-skype/