In March 2026, researchers uncovered Darksword malware, a powerful exploit targeting iPhones through compromised Ukrainian websites. This spyware, designed to steal data and cryptocurrency, is the second major iPhone attack in a single month, following the discovery of Coruna spyware. These incidents highlight a troubling trend: advanced cyber tools, once limited to state-level intelligence, are now accessible to criminal networks.
For organizations relying on traditional security measures like encryption, updates, and centralized servers, this development is a critical warning. Encryption alone is no longer enough when malware operates at the OS level, bypassing protections to access microphones, locations, and screen activity. The question is no longer if your devices will be targeted, but when and whether your defenses are ready.
At ARMA Instruments, we advocate for a fundamental shift in security: eliminating the attack surface entirely. The Darksword threat underscores the urgency of this approach. Below, we examine the risks, the limitations of conventional security, and how zero-trust architecture can secure your communications for the future.
The Darksword Threat: What Happened?
Researchers from Lookout, iVerify, and Google identified Darksword on servers linked to previous cyberattacks. The malware exploits vulnerabilities in iOS versions 18.4 to 18.6.2, potentially affecting 220 to 270 million iPhones, many of which remain unpatched despite Apple’s fixes.
Key Findings
- Darksword was distributed via Ukrainian websites, indicating geopolitical or opportunistic motives.
- The commercialization of spyware tools, previously restricted to state actors, now extends to criminal groups.
- Poor operational security in Darksword’s deployment suggests attackers are less concerned about exposure, likely due to easy access to replacements.
Why This Matters for Enterprises
- Metadata Risks: Spyware doesn’t just steal content; it harvests metadata, location data, and behavioral patterns, which can be even more damaging.
- Legal and Reputational Consequences: Compromised devices can lead to compliance violations, data leaks, and loss of trust.
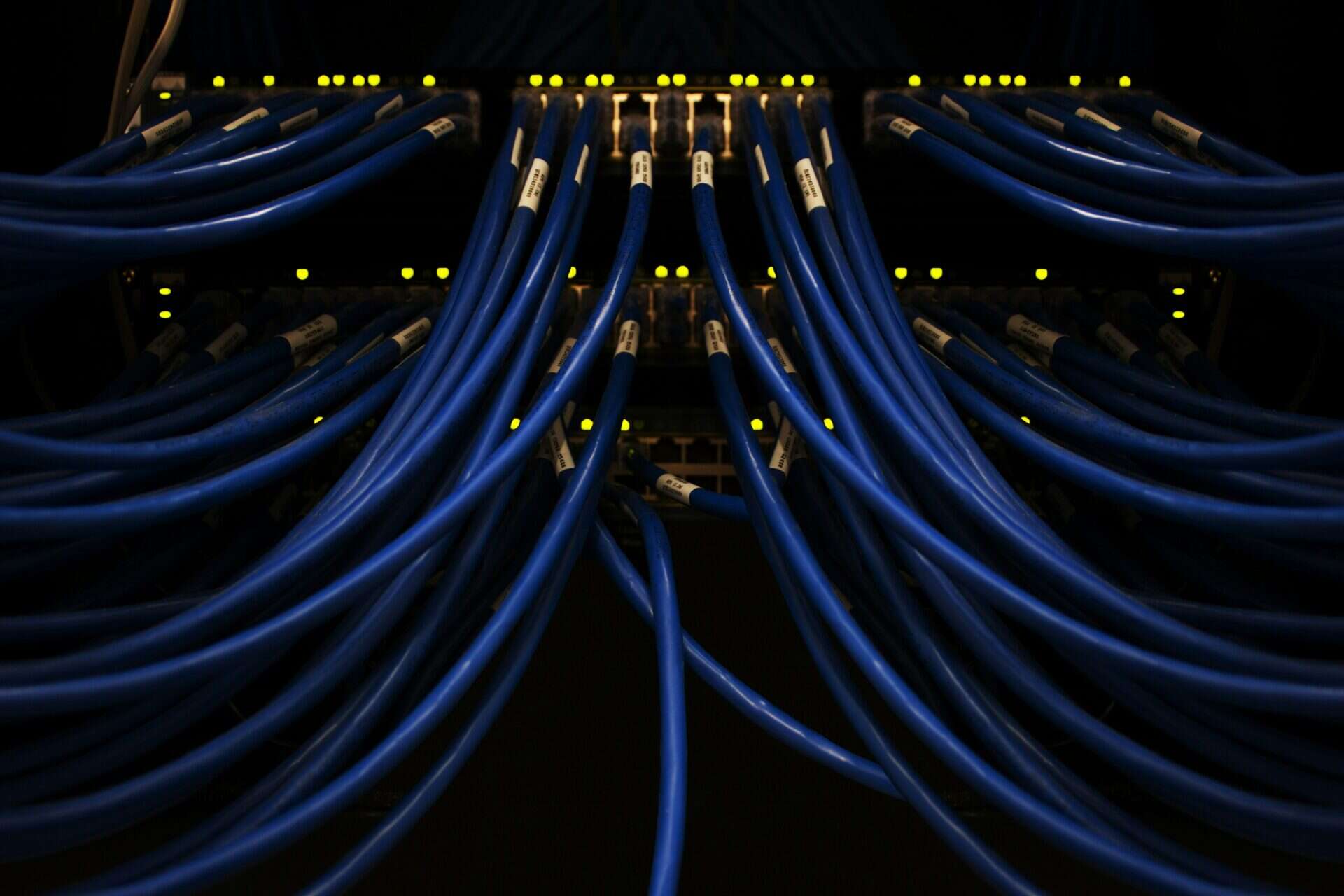
The Flaw in Traditional Security Models
Most organizations still depend on a castle-and-moat security approach:
- Encryption protects data in transit.
- Firewalls and updates guard against known threats.
- Centralized servers manage authentication and storage.
However, Darksword reveals critical weaknesses in this model:
- Encryption is ineffective when malware gains OS-level access.
- Central servers act as honey pots, attracting hackers and legal pressures.
- Static identifiers, such as phone numbers and IPs, create permanent targets for attackers.
The result is a false sense of security and an increasing number of high-profile breaches.
ARMA’s Zero-Trust Solution: Security by Design
At ARMA, we don’t just address threats, we remove the attack surface. Our architecture is built on three core principles:
Dynamic Identity: No Static Targets
Traditional systems rely on permanent identifiers like phone numbers and emails, which are easy to track and exploit. ARMA replaces these with ephemeral, rotating identities, ensuring no long-term exposure.
Serverless Architecture: No Central Points of Failure
Central servers are single points of failure, making them attractive targets for hackers and legal pressures. ARMA’s decentralized, serverless design ensures no sensitive data is stored in one place, reducing the risk of breaches and legal exposure.
Post-Quantum Cryptography: Future-Proof Protection
Even the strongest encryption can be compromised by quantum computing. ARMA’s post-quantum algorithms ensure your communications remain secure against tomorrow’s threats.
Why This Matters for High-Risk Organizations
For governments, NGOs, and enterprises handling sensitive data, the risks are significant:
- Geopolitical escalation: State-linked attacks, such as those involving Darksword in Saudi Arabia, Turkey, and Malaysia, can disrupt operations or leak critical intelligence.
- Compliance risks: Failures to protect data can result in fines, lawsuits, and reputational damage.
- Operational resilience: In times of crisis, trust in your tools is essential.
ARMA’s solution represents more than an upgrade. By eliminating permanent servers and static identifiers, we ensure that even if a device is compromised, the attacker gains nothing.
The Bottom Line: Act Now
The discovery of Darksword is not an isolated incident; it reflects the new reality of cyber threats. Organizations that fail to adapt will be outmaneuvered by increasingly sophisticated and accessible threats.
Consider this:
- Are your communications truly secure, or are you relying on outdated assumptions?
- Can your current tools defend against OS-level spyware like Darksword?
- Are you prepared for the legal, financial, and reputational consequences of a breach?
Next Steps
- Assess Your Risk: Evaluate your current security for reliance on static identifiers or central servers.
- Explore Zero-Trust: Learn how ARMA’s dynamic identity and serverless architecture can protect your organization.
- Future-Proof Your Defenses: Contact us to discuss post-quantum cryptography and resilience against evolving threats.