The Invisible Chain: How Static Identifiers Expose You
Your phone is not just a device, it’s a beacon. Every call, message, or authentication tied to a static identifier, whether a phone number, IMSI, or IMEI, creates a permanent link between you, your device, and your physical location. This link is a privacy concern and a critical security flaw.
Adversaries, from cybercriminals to state-sponsored actors, exploit these static anchors to track, profile, and target individuals. Traditional secure communication tools, even those claiming to be “encrypted,” often fail to address this fundamental vulnerability. The result? Users remain exposed to surveillance, metadata exploitation, and real-world threats.
The Problem: Static Identifiers as a Single Point of Failure
1. Permanent Exposure
Phone numbers and IMSI/IMEI identifiers have been tied to individuals for years, creating a persistent trail of metadata. This data can be correlated across platforms, locations, and time, revealing patterns of behavior, associations, and even physical movements.
2. Targeted Attacks
Once exposed, static identifiers become anchors for surveillance. Spyware (e.g., Pegasus, Predator), IMSI-catchers, and SS7-based attacks all rely on the predictability of these identifiers to locate, monitor, and compromise targets.
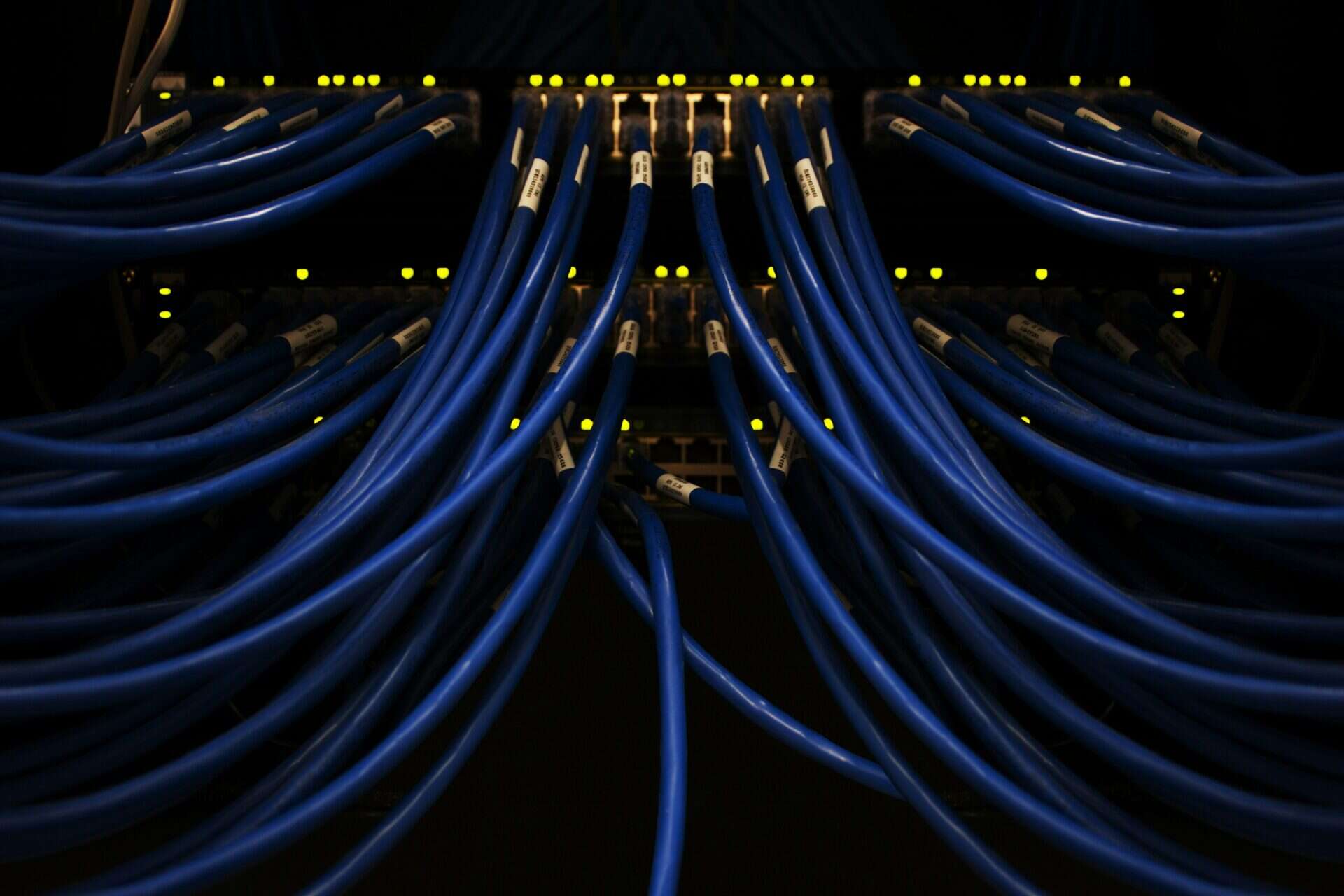
3. Legacy Systems, Modern Risks
Most secure communication tools still depend on phone numbers or email addresses, inheriting their flaws. In an era of advanced spyware and AI-driven surveillance, static identifiers are outdated and very dangerous.
Static vs. Dynamic Identity: A Comparison
Static vs. Dynamic Identity
| Feature | Static Identity (Traditional) | Dynamic Identity (ARMA G1) |
| Identifier Type | Fixed (phone number, IMSI, IMEI) | Rotating, ephemeral |
| Traceability | High (easy to track over time) | Low (no persistent anchors) |
| Surveillance Risk | High (vulnerable to IMSI-catchers, spyware) | Minimal (identifiers shift dynamically) |
| Metadata Exposure | Extensive (correlatable across platforms) | Limited (obscured patterns) |
| Attack Surface | Broad (static anchors for exploits) | Narrow (no fixed targets) |
| Operational Freedom | Limited (risk of tracking/compromise) | High (true anonymity and safety) |
ARMA’s Solution: Dynamic Identity
ARMA Instruments severs the link between user, device, and location with Dynamic Identity, a core feature of the ARMA G1 secure communication platform.
How It Works
- No Fixed Anchors: Identifiers shift dynamically, preventing long-term correlation or tracking.
- Reduced Traceability: Communication patterns become significantly harder to profile, even under legal or adversarial pressure.
- Architectural Priority: Identity isn’t an afterthought, it’s a security boundary. By design, ARMA eliminates the risks of static identifiers.
Why It Matters
For leaders, diplomats, and high-risk professionals, Dynamic Identity is a necessity. It ensures that users cannot be tracked, profiled, or located through standard telecom methods, providing true operational freedom.
The Future of Secure Communication
As quantum computing and AI advance, the ability to obscure identity will define secure communication. Dynamic Identity doesn’t just add a layer of security, it removes the vulnerability entirely.
Key Benefits
- For Individuals: Lower risk of impersonation, stalking, or targeted compromise.
- For Organizations: Protection against metadata-based attacks, which often precede breaches or espionage.
- For the Future: A proactive approach to security in an era of evolving threats.
Is your organization still relying on static identifiers? Explore ARMA G1’s Dynamic Identity or contact us to learn how to eliminate this flaw from your communications.