Imagine a massive mail sorting center through which millions of letters pass every day. Each envelope may be sealed, but the facility still handles them all: routing, scanning addresses, storing them temporarily in vast bins. For efficiency, everything flows through this one place.
Now imagine an adversary gaining quiet access to that facility. They don’t need to open the letters today. They simply copy them, catalog the senders and recipients, and store the envelopes for later. One day, when better tools or legal pressure make it possible, those letters can be opened.
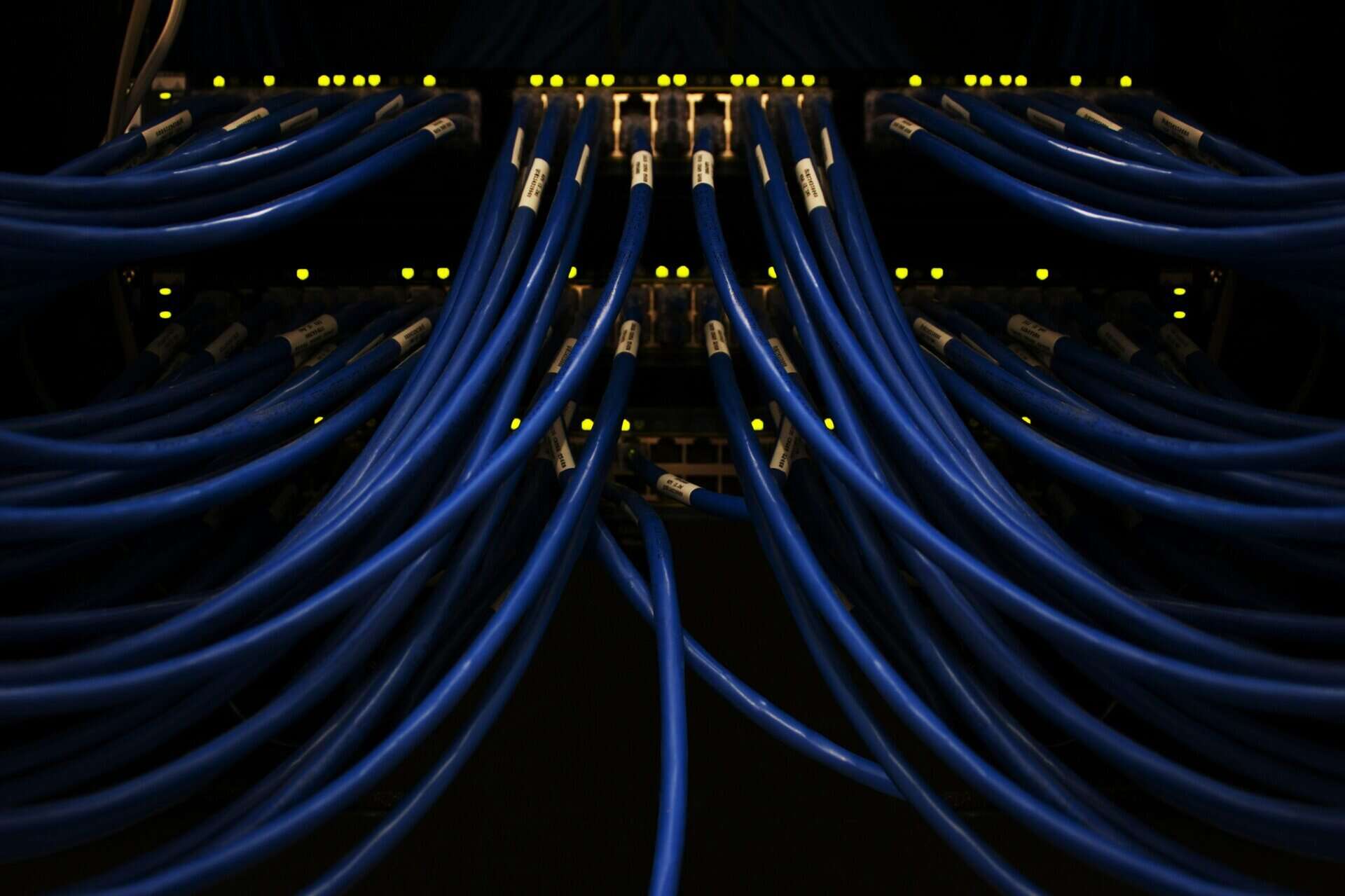
This is effectively how modern communication infrastructure works. Centralized messaging servers are designed for efficiency and reliability, but in doing so they concentrate encrypted messages, metadata, and social graphs into a handful of highly valuable targets.
The risk is not theoretical. The SolarWinds breach demonstrated how even well-defended, compliant systems can be quietly compromised, turning trusted infrastructure into long-term intelligence collection platforms. In a world of “harvest now, decrypt later,” the mere existence of these centralized troves has become a strategic vulnerability.
Another incident show how central servers in secure communications posed risks. In 2025, a modified Signal-based app used by U.S. officials was breached, exposing archived messages due to central storage. Also, messaging apps that collect metadata centrally make it easier for attackers to analyze communication patterns. Both cases show how central storage creates long-term vulnerabilities.
At ARMA Instruments, we eliminate this risk by design. Our serverless architecture ensures that sensitive communication data is never stored in a central place, removing the target for both today’s attackers and tomorrow’s decryption efforts. Because in the end, the safest data is the data that was never collected in the first place.
The Problem: Central Servers as High-Value Targets
Central servers aggregate metadata, who communicates with whom, when, and from where. This data, even when encrypted, reveals patterns, relationships, and intent. For adversaries, it’s a goldmine; for institutions, it’s a systemic vulnerability.
Attracting attackers high-profile breaches (e.g., SolarWinds, Microsoft Exchange) prove that centralized systems are magnets for state-sponsored and criminal actors. The more valuable the data, the more relentless the attacks.
The illusion of control, even “secure” providers with robust encryption, cannot eliminate the risk of insider threats, misconfigurations, or third-party exploits. Centralization creates single points of failure, by design.
ARMA’s Solution: Serverless by Design
ARMA Instruments eliminates this liability architecturally, not just operationally:
No permanent servers: Communication data is never stored on central servers, removing the primary target for attackers and litigators.
Dynamic Identity: Without static identifiers (e.g., phone numbers), metadata correlation becomes exponentially harder.
Post-Quantum Cryptography: Ensures long-term confidentiality, even against future threats.
Resilience Under Pressure: Reduces exposure to large scale breaches, subpoenas, and geopolitical manipulation.
The safest data is the data that was never stored and the most secure infrastructure is the one that doesn’t exist as a target.
Why This Matters for Institutions
Governments & Diplomats: Limit exposure to espionage and reduce leverage points for adversarial states.
CISOs & Enterprises: Avoid reputational and financial fallout from breaches tied to centralized data stores.
NGOs & High-Risk Individuals: Operate in hostile environments without fear of metadata driven profiling or coercion.
A Call to Rethink Secure Communication
Security is not about building higher walls around vulnerable systems. It’s about removing the vulnerabilities themselves. In a world where central servers have become strategic liabilities, the only forward is to design them out.
Is your organization still betting its resilience on architecture from the past? Explore ARMA’s serverless solutions or request a demo to see how zero-trust communication works in practice.