Since March 23, 2026, Hong Kong’s border officials have had the legal power to demand travelers’ phones and laptops, inspect their contents, and copy data without a warrant. This policy, introduced under the pretext of national security, reflects a global trend: border controls are becoming more intrusive, and your privacy is at risk.
The problem isn’t just about Hong Kong. From the U.S. to China, governments are increasingly seizing devices, accessing private data, and leaving travelers with no recourse. Traditional security measures like encryption and passwords offer no protection when your device is physically confiscated.
At ARMA Instruments, we believe privacy shouldn’t end at the border. Our zero-trust architecture ensures your communications remain secure, even when your device isn’t.
The Reality: Your Privacy Ends at the Border
The Het Financiële Dagblad article highlights how Hong Kong’s new policy allows officials to:
- Demand access to phones and laptops from any traveler, without suspicion.
- Copy data including messages, photos, and contacts without transparency.
- Detain travelers who refuse to comply, even if they have nothing to hide.
This isn’t an isolated case. In the U.S., border agents can search devices without a warrant. In China, travelers face mandatory app installations that scan their data. The message is clear: your phone isn’t yours when you travel.
Why This Matters
- No Control Over Your Data: Once your phone is seized, you have no idea where your data goes or who accesses it.
- Metadata Risks: Even encrypted messages reveal who you talk to, where you’ve been, and what you do information that can be weaponized.
- Legal Consequences: Refusing to unlock your device can lead to detention, fines, or even criminal charges in some countries.
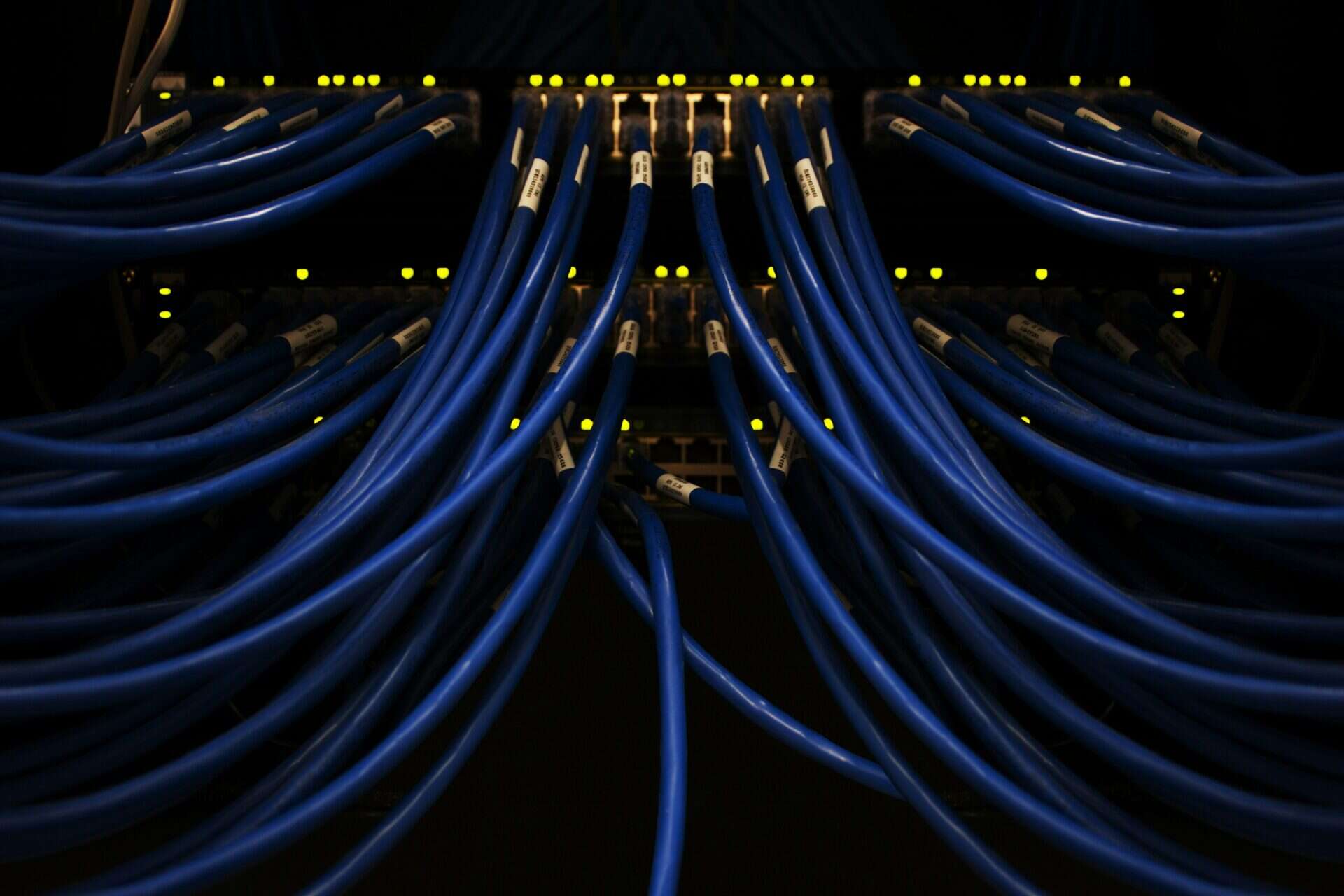
The Flaw in Traditional Security
Most organizations rely on encryption, passwords, and centralized servers to protect data. But these measures fail when:
- Devices are physically seized (encryption doesn’t stop officials from copying data).
- Metadata is exposed (your contacts, location history, and app usage are still visible).
- Central servers are vulnerable (governments can subpoena or hack them).
Hong Kong’s policy is a wake-up call: if your security depends on controlling your device, it’s not real security.
ARMA’s Solution: Zero-Trust Communication
At ARMA, we eliminate the attack surface by design. Our platform ensures:
✅ Dynamic Identity: No static phone numbers or IMSI codes to trace or copy.
✅ Serverless Architecture: No central servers to seize or subpoena.
✅ Post-Quantum Encryption: Even if your device is confiscated, your messages remain unreadable.
The Bottom Line: Privacy Shouldn’t End at the Border
Hong Kong’s policy isn’t an outlier it’s a preview of a future where privacy is conditional. Organizations that rely on traditional security will find themselves exposed.
Ask yourself:
- Can your current tools protect your data if your phone is seized?
- Are you prepared for the legal and reputational risks of border searches?
- Do you trust governments or hackers with your most sensitive information?
At ARMA, we don’t just answer these questions we eliminate them by design.
Next Steps
- Assess Your Risk: Audit your current security for reliance on physical devices or central servers.
- Explore Zero-Trust: Learn how ARMA’s dynamic identity and serverless architecture can protect your team.
- Future-Proof Your Privacy: Contact us to discuss how ARMA keeps your communications secure no matter where you travel